새로운 배포는 Tor 브라우저 10.5에 도입된 기능을 기반으로 하여 검열이 심한 지역에서 Tor에 접속하는 사용자 경험을 바꾸었어요.
신규 기능

자동 검열 감지 및 우회
작년 Tor 브라우저 10.5의 출시와 함께 Tor 런처의 사용 중지와 브라우저 창 접속 흐름의 통합과 같이 Tor 연결 경험을 새롭게 만들었어요.
그러나 Tor 네트워크 자체에 대한 검열 우회가 여전히 수동적이고 혼란스러운 과정으로 남아 있었기에 사용자는 Tor 네트워크 설정에서 Tor 차단 해제를 위한 브리지 적용법을 직접 알아내야 했어요.
더욱이 Tor에 대한 검열은 획일적이지 않으므로, 특정 장착형 전송수단 또는 브리지 설정이 한 국가에서는 작동할 수 있지만 그 밖의 국가에서는 작동하지 않을 수도 있어요.
이로 인해 (이미 상당한 압박을 받고 있을) 검열 대상 사용자가 어떤 옵션을 선택해야 할지 알아내야 하는 부담이 가중되었고, 그 과정에서 많은 시행착오와 좌절을 경험하게 되었어요.
이러한 부담을 줄이기 위해 Tor 프로젝트 반검열팀과 협력하여, 필요할 때 현재 위치에 가장 적합하다고 생각되는 브리지 설정을 자동으로 적용할 수 있는 새로운 기능인 접속 도우미를 도입했어요.
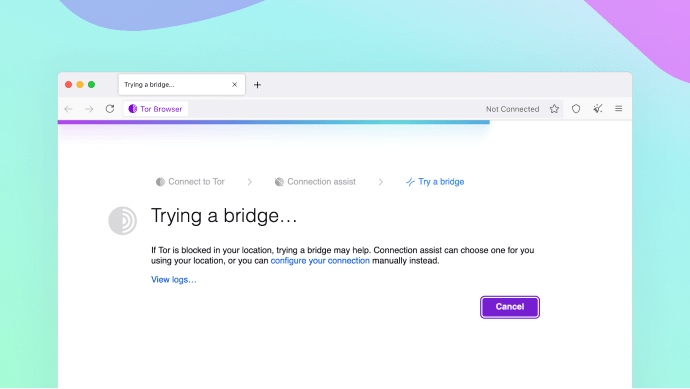
접속 도우미는 사용자의 동의 하에 위치를 사용할 수 있도록 국가별 옵션의 최신 목록을 조회하고 다운로드하는 방식으로 작동해요.
Tor 브라우저가 torproject.org에서 브리지를 요청하는 데 사용하는 것과 동일한 도메인 프론팅 도구인 moat를 사용하여 Tor 네트워크에 먼저 연결할 필요 없이 이를 수행해요.
접속 도우미가 첫 번째 안정적인 배포라는 이정표에 도달했지만, 아직 버전 1.0에 불과하므로 향후 배포에서 사용자 환경을 개선하려면 피드백이 매우 중요해요.
Tor 네트워크가 차단될 수 있는 국가(예: 벨라루스, 중국, 러시아, 투르크메니스탄)의 사용자는 알파 테스터로 자원봉사하거나 Tor 포럼에 결과를 보고하여 이 기능의 최신 버전을 테스트할 수 있어요.
재설계된 Tor 네트워크 설정
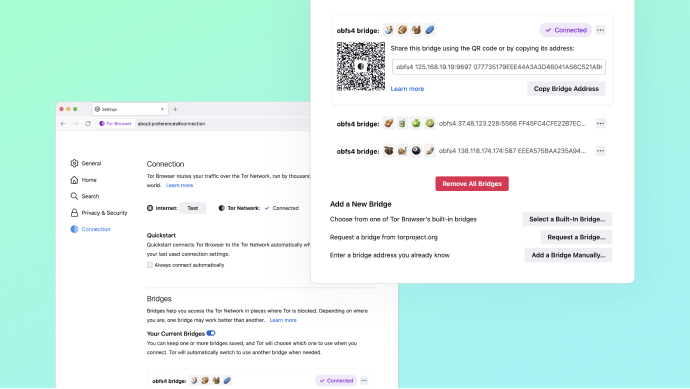
극심한 검열 하에 있는 대다수 사용자가 접속 도우미 덕분에 버튼 하나만 눌러 Tor에 접속할 수 있었으면 좋겠네요.
그러나 항상 예외가 있다는 것을 알고 있고, 많은 사용자가 접속을 수동 구성하는 것을 선호해요.
그렇기 때문에 Tor 네트워크 설정을 다음과 같이 재설계하는 데 시간을 투자했어요:
- 새로운 이름: Tor 네트워크 설정은 이제 접속 설정이라고 해요. 이는 탭에서 어떤 설정을 찾을 수 있는지 명확히 하기 위한 거예요.
- 접속 상태: 접속 문제의 원인을 해결하는 데 도움이 되도록, moat를 사용하여 Tor 없이 인터넷 접속을 테스트하는 옵션이 포함된 마지막으로 알려진 접속 상태를 탭 상단에서 찾을 수 있게 되었어요.
- 간소화된 브리지 옵션: 필드와 옵션의 긴 목록이 사라졌어요. 새 브리지를 추가하는 각 방법은 개별 대화상자 메뉴로 정리되어 향후 추가 개선 사항을 지원하는 데 도움이 될 수 있어요.
- 접속 도우미: 검열이 의심되어 Tor 브라우저에서 Tor 네트워크에 접속할 수 없는 경우, 브리지를 선택할 수 있는 추가 옵션을 자동으로 사용할 수 있게 돼요.
- 새로운 브리지 카드: 브리지는 설정이 끝나도 거의 보이지 않았어요. 이제 저장된 브리지가 브리지 공유를 위한 새로운 옵션과 함께 편리한 브리지 카드 스택에 표시돼요.
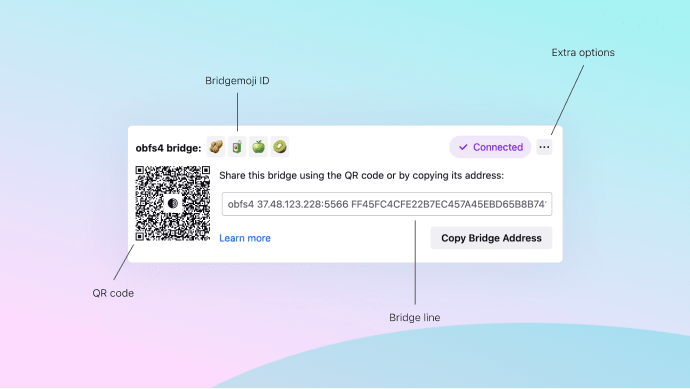
이는 확장했을 때의 브리지 카드 구조예요. 브리지 라인을 복사하고 공유하는 것 외에도 각 브리지에는 향후 배포에서 안드로이드용 Tor 브라우저(다른 Tor 기반 앱도 해당함)에서 읽을 수 있는 고유한 QR 코드가 함께 제공되어 작동하는 브리지를 데스크톱에서 모바일로 쉽게 전송할 수 있게 해 줘요.
여러 브리지를 설정하면 카드가 스택으로 축소되는데, 각 브리지는 클릭 한 번으로 다시 확장할 수 있어요.
접속된 경우 Tor 브라우저는 보라색 "✔ 접속됨" 알약과 함께 현재 사용 중인 브리지를 알려줘요.
길고 비우호적인 브리지 라인을 비교할 필요 없이 브리지를 구별할 수 있도록, 적합한 브리지를 한 눈에 식별하는 데 사용할 수 있는 짧은 4개의 이모티콘 시각화 기술인 bridge-moji를 도입했어요.
마지막으로, 접속 설정 내의 도움말 링크는 이제 오프라인에서도 작동해요. 간단하게 정리하자면, Tor 브라우저 설정에는 support.mozilla.org를 가리키는 링크와 tb-manual.torproject.org를 가리키는 도움말(예: Tor 브라우저 매뉴얼)의 두 가지 유형의 도움말 링크가 있어요.
그러나 웹 기반 링크는 Tor 브라우저 접속 문제를 해결할 때 그다지 유용하지 않았으므로, Tor 브라우저 11.5에는 오프라인에서도 사용할 수 있는 매뉴얼이 포함되어 있어요.
Tor 브라우저 설정 내의 도움말 링크 외에도 응용프로그램 메뉴 > 도움말 > Tor 브라우저 매뉴얼 또는 브라우저 주소 표시줄에 "about:manual"을 입력해서 매뉴얼을 볼 수 있어요.
HTTPS 전용 모드, 기본값
HTTPS-Everywhere는 이전에 Tor 브라우저에 번들로 제공되었던 두 가지 확장 프로그램 중 하나이며, 가능한 한 연결을 HTTPS로 자동 업그레이드하여 사용자를 보호하도록 오랜 기간 탁월한 경력을 쌓아왔어요.
이제 HTTPS는 어디에나 적용되어 있고, 모든 주요 웹 브라우저는 HTTPS로 자동 업그레이드되도록 기본적으로 지원해요.
Tor 브라우저의 기반이 되는 기본 브라우저인 Firefox는 이 기능을 HTTPS 전용 모드라고 불러요.
Tor 브라우저 11.5부터 데스크톱에서 HTTPS 전용 모드가 기본적으로 활성화되며 HTTPS-Everywhere는 더 이상 Tor 브라우저 번들로 제공되지 않아요.
왜 하필 지금인가요? Mozilla 연구에 따르면 일반 사용자가 방문하는 안전하지 않은 페이지의 비율은 매우 낮아 사용자 경험에 발생하는 혼란이 별로 없어요.
또한 이러한 변경은 악의적인 출구 중계기에 의한 SSL 스트리핑 공격으로부터 사용자를 보호하는 데 도움이 되며, 처음부터 중간자 공격을 위해 출구 중계기를 가동할 동기를 크게 줄였어요.
HTTPS-Everywhere가 Tor 브라우저의 두 번째 목적이기도 했으며 SecureDrop에서 사람이 읽을 수 있는 어니언 이름이 작동하도록 하는 데 일부 책임이 있다는 사실을 이미 알고 계시거나, 아니면 모르고 계셨던 분들도 있으실 거예요.
SecureDrop 사용자는 HTTPS-Everywhere가 없을 때에도 사람이 읽을 수 있는 어니언 이름이 계속 작동하도록 Tor 브라우저를 패치했으므로 안심하셔도 괜찮아요.
참고: 단기적으로 안드로이드용 Tor 브라우저는 데스크톱과 달리 HTTPS-Everywhere를 계속 사용할 거예요. 아래 안드로이드에 대한 별도 업데이트를 참조하세요.
향상된 폰트 지원
Tor 브라우저에는 많은 핑거프린팅 방어 기능이 탑재되어 있는데, 악의적 사용자가 시스템에 설치된 글꼴을 사용하여 핑거프린팅할 수 있는 글꼴 열거로부터 보호하는 기능도 있어요.
이에 대응하기 위해 Tor 브라우저는 시스템에 설치된 글꼴 대신 사용할 수 있는 표준화된 글꼴 번들과 함께 제공돼요.
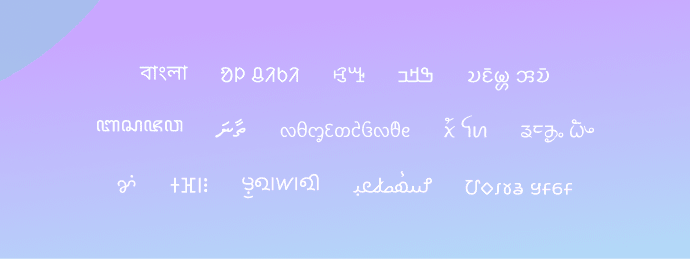
그러나 일부 스크립트 작성은 올바르게 렌더링되지 않았고 다른 스크립트는 Tor 브라우저에서 사용할 수 있는 글꼴이 전혀 없었어요.
이 문제를 해결하고 Tor 브라우저에서 지원하는 문자 체계 수를 확장하기 위해 이번 배포에서는 Noto family의 더 많은 글꼴을 번들로 제공해요.
당연한 말이지만, 설치 프로그램의 크기를 너무 많이 늘리지 않으면서 Tor 브라우저가 지원하는 글꼴 수 사이의 균형을 찾기 위해 신경쓰고 있어요.
따라서 Tor 브라우저에서 특정 언어의 문자가 올바르게 렌더링되지 않는다면 알려주셔야 해요!
피드백을 보내주세요
버그를 발견했거나 이 배포를 개선할 수 있는 방법에 대한 제안이 있는 경우 알려주세요.
이 배포에 기여한 모든 Tor 팀과 자원봉사자분들께 감사드려요.